What Is the Most Common Central Device Used Today to Connect Computers to a Network?
Computer Networks - options
Networks are collections of computers, software, and hardware that are all continued to help their users piece of work together. A network connects computers by ways of cabling systems or wireless connectivity, specialized software, and devices that manage data traffic. A network enables users to share files and resources, such as printers, as well every bit send messages electronically (electronic mail) to each other.
Computer networks autumn into two master types: client/server networks and peer-to-peer networks. A client/server network uses ane or more dedicated machines (the server) to share the files, printers, and applications. A peer-to-peer network allows any user to share files with any other user and doesn't require a central, defended server.
The almost mutual networks are Local Area Networks or LANs for short. A LAN connects computers within a single geographical location, such equally i office building, function suite, or domicile. By contrast, Wide Surface area Networks (WANs) span different cities or fifty-fifty countries, using phone lines or satellite links.
If you demand aid with your network and then give usa a call to find out more.
Typical home network (basic)
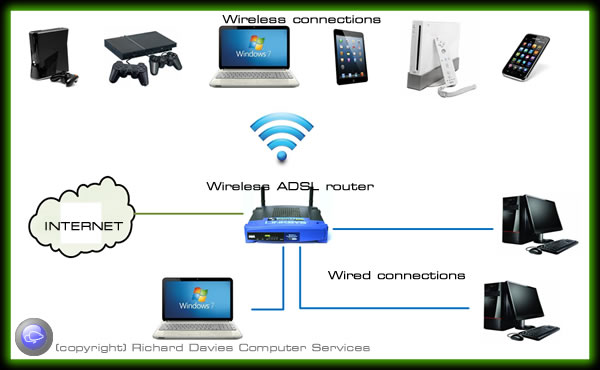 Typically you lot volition take a router to connect y'all to broadband. This volition share the internet connection with multiple devices using a combination of wired and wireless. Some routers don't have wireless built in so you may need an additional slice of equipment or upgrade your router to a wireless ADSL (broadband) router such equally the Netgear DGN2000. Nigh ADSL routers have only 4 network ports. If you have more than this (including network printers) you volition need an additional network switch to extend the number of ports.
Typically you lot volition take a router to connect y'all to broadband. This volition share the internet connection with multiple devices using a combination of wired and wireless. Some routers don't have wireless built in so you may need an additional slice of equipment or upgrade your router to a wireless ADSL (broadband) router such equally the Netgear DGN2000. Nigh ADSL routers have only 4 network ports. If you have more than this (including network printers) you volition need an additional network switch to extend the number of ports.
With a combined network/wireless router in place continued to an ADSL connexion all you demand to do is connect your device to the router using a wire or wirelessly.
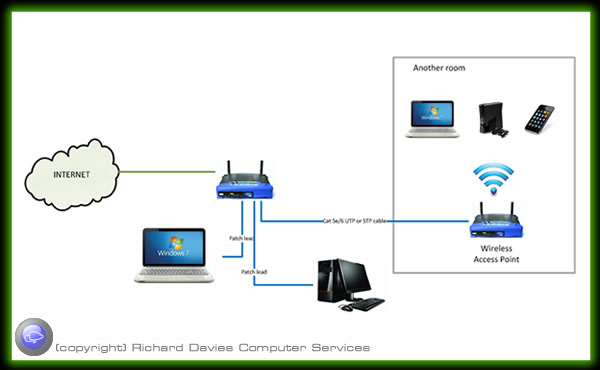
Depending on the size of your home, the thickness of walls and interference from other devices yous may need to extend your network further so that you can have wireless or wired connections in all rooms.
Wireless Access Indicate
Wireless access points (APs or WAPs) are specially configured nodes on wireless local area networks (WLANs). Access points human activity as a primal transmitter and receiver of WLAN radio signals.
Access points used in dwelling house or small business networks are generally small, dedicated hardware devices featuring a built-in network adapter, antenna, and radio transmitter. Access points support Wi-Fi wireless communication standards.
Although very small WLANs tin can function without access points in and so-called "ad hoc" or peer-to-peer fashion, access points support "infrastructure" way. This manner bridges WLANs with a wired Ethernet LAN and also scales the network to support more clients.
Why wireless 300n is all-time.
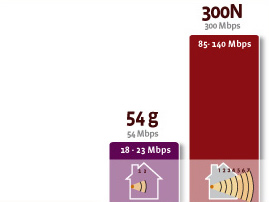 What is the difference betwixt "one thousand" and "n"?
What is the difference betwixt "one thousand" and "n"?
There are a number of standards for wireless networks (802.11b, a, 1000 and n). The "n" standard is the latest and fastest of these. The "n" standard distinguishes itself from its predecessor "g" by offering a wireless speed which is upwards to 12 times faster and a range which is upwards to four times greater.
What is the advantage of n?
Present, wireless networks are not only used to surf the Internet or to send due east-mails. With the 802.11n draft two.0 solutions, users can bask unprecedented performance in terms of speed and range for demanding applications, such as streaming Hd audio and video, Vox over IP, multiplayer gaming and transferring large quantities of information. "N" meets the demand for faster wireless speeds and delivers impressive performance when, for example, downloading files, viewing videos on YouTube or playing your favourite online games with speeds of up to 300 Mbps.
Why is it and then easy?
With "n", you savour unprecedented operation in environments with multiple users and demanding applications.
The 300N solutions are backwards compatible and tin be used in combination with 802.11b/k devices.
Wireless Repeater (extender)
For this you demand a wireless repeater or extender. A wireless range extender increases the distance over which a WLAN signal can spread, overcoming obstacles and enhancing overall network betoken quality.
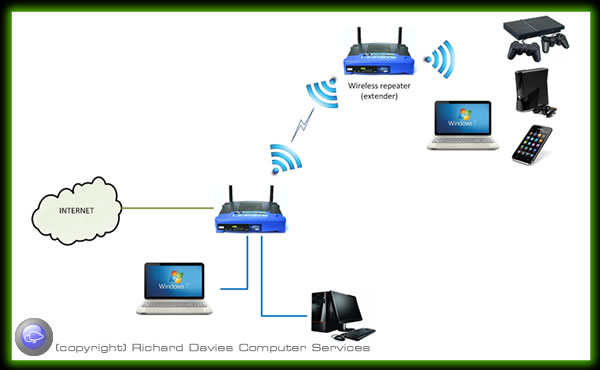
Several different forms of wireless range extenders are available. These products are sometimes called "range expanders" or "signal boosters." A wireless range extender works as a relay or network repeater, picking upwards and reflecting WiFi signals from a network'southward base router or access signal.
The network performance of devices connected through a range extender volition generally be lower than if they were continued directly to the chief base station.
A wireless range extender connects via Wi-Fi to a router or access point. However, due to the nature of this applied science, almost wireless range extenders work only with a limited ready of other equipment.
Network Powerline adaptors
Alternatively you can utilize powerline adaptors which use your electric mains to communicate through without the demand of additional network wiring.
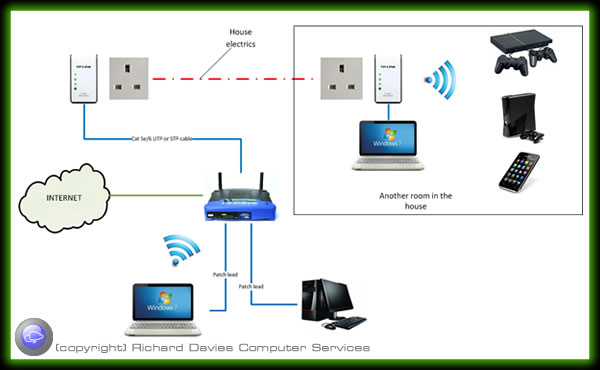

You don't need to stick to only one blazon of network extension type, you can adopt a combination of different methods to achieve full network coverage.

Business network topography
Depending on number of machines you need to connect y'all need to decide whether you are going to configure as a peer to peer network or a domain driven network using a server/due south. Take a look at our server page for information nigh the divergence between them. The rule of pollex is; if y'all require security, require your ain email exchange, accept remote workers any have more than near vi Pc's you may crave a server driven (domain) network.

If y'all need help with your network then requite us a phone call to find out more.
Multiple offices
Same rules apply as for a pocket-size office; choose betwixt peer to peer and domain. Depending on the number of network connections needed yous may need a data cabinet to house the cables from all the network wall ports, the router and switches.
Offices can be continued together using Cat5e/6 cabling back to the data cabinet/switch. Information technology the offices are in different buildings but in line of sight it is possible to link the buildings together using wireless, alternatively you can configure a VPN (Virtual Private Network) using the net every bit a conduit.
Note: Cat 6 (UTP = Unshielded Twisted Pair) (STP = Shielded Twisted Pair). Cat 5e UTP is fairly inexpensive to buy and is adequate for virtually network wiring, all the same if you lot crave Gigabit (1000Mbit network speed) to piece of work effectively and so Cat6 will be required. STP protects the cable from cantankerous talk (interference from other cabling) and therefore better for longer cable runs and where the cablevision passes electrical cables etc.
Networking that require loftier speed (Gigabit etc), components must exist consistent throughout the network east.grand. Gigabit switch, Gigabit wiring and Gigabit network interfaces on PC'due south / Laptops etc.
Public WiFi

Your Responsibilities as a WiFi hotspot owner
Whether you run a small bed and breakfast or a large 5 star hotel, if y'all're operating a WiFi hotspot, you demand to be enlightened of, and compliant with, all relevant laws and legislation regarding their operation.
There are various laws and pieces of legislation that apply to the operation of public WiFi hotspots in the Britain. These laws cover things like copyright infringement, accessing of illegal content, e-mail spam, hacking and all sorts of other questionable action. If you're running a public WiFi hotspot, you need to be able to make sure you are compliant with these laws.
Tracking Usage
The commencement matter you need to be able to exercise is identify who is using your network, so that y'all can track activity and keep a record in case the authorities inquire you to provide them with information regarding any incident traced back to your network. This is very difficult to do unless you take the proper infrastructure, every bit a basic, unsecured, public WiFi hotspot volition not cater for this, and each user will effectively be anonymous. RDCS' Hotel WiFi service can provide you with everything y'all need to track usage.
Content Filtering
If you're offer a Hotel WiFi Hotspot and want to fully compliant with the law, information technology's a lot easier to practise if you lot filter the content users are looking at. RDCS tin can offer a content filtering service that prevents users from accessing illegal or questionable content.
Digital Economy Bill
The recently introduced Digital Economy Nib (DEB) has made information retention and usage tracking even more important. This bill, along with a few other things, covers copyright infringement and the unlawful downloading of copyrighted content online. If your public WiFi hotspot users are carrying out this action on your network and you aren't at to the lowest degree tracking usage, y'all could stop up getting hit with a hefty fine even though you weren't directly responsible. Our system can record all activity on your hotspot and trace it back to the individual device and account that was used to admission the content.
RDCS Public WiFi organisation
Typical layout for the Hot Spot system (shown in crimson on the figure beneath). Multiple Wireless Access Points and network connections can be connected to the hot spot organisation and separated from your individual network whilst sharing the same ADSL connexion.
Depending on the configuration guests can log on without providing any details subsequently accepting the terms and weather condition, alternatively you could specify any number of details you require from the guest or fifty-fifty charge for access. In either instance details are logged of the session against the mac address and IP of the connected devices. Bandwidth throttling and website filtering can too be configured.
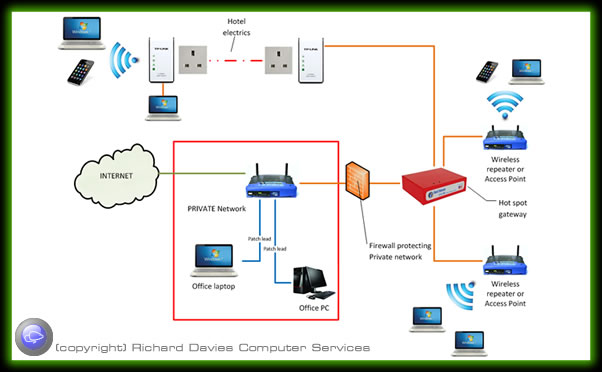
Contact u.s. on 01822 810799 if you would like to know more.
Terminology - the short listing
ADSL
ADSL (Asymmetric Digital Subscriber Line) is a technology for transmitting digital data at a high bandwidth on existing phone lines to homes and businesses. Unlike regular dialup phone service, ADSL provides continuously-available, "always on" connectedness. ADSL is asymmetric in that it uses about of the channel to transmit downstream to the user and only a small function to receive data from the user. ADSL simultaneously accommodates analogue (voice) information on the same line. ADSL is mostly offered at downstream data rates from 512 Kbps to about 6 Mbps.
Power Over Ethernet (POE)
Power over Ethernet (PoE) is a technology for wired Ethernet LAN's(local area networks) that allows the electrical current necessary for the operation of each device to be carried by the information cables rather than by ability cords. Doing then minimizes the number of wires that must exist strung in gild to install the network. The result is lower price, less reanimation, easier maintenance, and greater installation flexibility than with traditional wiring.
For PoE to work, the electrical electric current must go into the information cable at the ability-supply end, and come up out at the device end, in such a way that the current is kept separate from the information signal then that neither interferes with the other. The current enters the cablevision past ways of a component called an injector. If the device at the other stop of the cable is PoE compatible, then that device volition function properly without modification. If the device is not PoE compatible, and then a component called a picker or tap must be installed to remove the current from the cable. This "picked-off" current is routed to the power jack.
To minimize the possibility of harm to equipment in the event of a malfunction, the more than sophisticated PoE systems employ fault protection. This feature shuts off the power supply if excessive current or a short circuit is detected.
Network Switch
A network switch is a small hardware device that joins multiple computers together within one local surface area network (LAN). Technically, network switches operate at layer two (Data Link Layer) of the OSI model.
Network switches announced nearly identical to network hubs, merely a switch more often than not contains more intelligence (and a slightly higher toll tag) than a hub. Unlike hubs, network switches are capable of inspecting information packets every bit they are received, determining the source and destination device of each bundle, and forwarding them appropriately. By delivering messages only to the connected device intended, a network switch conserves network bandwidth and offers mostly better performance than a hub.
Equally with hubs, Ethernet implementations of network switches are the nigh common. Mainstream Ethernet network switches back up either 10/100 Mbps Fast Ethernet or Gigabit Ethernet (x/100/one thousand) standards.
Different models of network switches support differing numbers of connected devices. Well-nigh consumer-grade network switches provide either 4 or 8 connections for Ethernet devices. Switches can be connected to each other, a then-chosen daisy chaining method to add progressively larger number of devices to a LAN.
LAN (Local Area Network)
A local expanse network (LAN) supplies networking capability to a group of computers in close proximity to each other such as in an role edifice, a schoolhouse, or a home. A LAN is useful for sharing resources like files, printers, games or other applications. A LAN in turn often connects to other LANs, and to the Internet or other WAN.
Most local area networks are built with relatively inexpensive hardware such as Ethernet cables, network adapters, and hubs. Wireless LAN and other more advanced LAN hardware options also be.
Specialized operating system software may be used to configure a local area network. For instance, near flavors of Microsoft Windows provide a software package called Internet Connection Sharing (ICS) that supports controlled admission to LAN resources.
The term LAN political party refers to a multiplayer gaming event where participants bring their ain computers and build a temporary LAN.
WAN
A broad expanse network (WAN) is a telecommunications network, usually used for connecting computers, that spans a wide geographical area. WANs can by used to connect cities, states, or even countries. WANs are often used by larger corporations or organizations to facilitate the exchange of data, and in a broad variety of industries, corporations with facilities at multiple locations take embraced WANs. Increasingly, however, fifty-fifty small businesses are utilizing WANs as a way of increasing their communications capabilities.
Although WANs serve a purpose similar to that of local area networks (LANs), WANs are structured and operated quite differently. The user of a WAN normally does not own the communications lines that connect the remote calculator systems; instead, the user subscribes to a service through a telecommunications provider. Unlike LANs, WANs typically do not link individual computers, simply rather are used to link LANs. WANs besides transmit data at slower speeds than LANs. WANs are as well structurally similar to metropolitan surface area networks (MANs), but provide communications links for distances greater than 50km.
Router
Network router is a device or a slice of software in a computer that forrad and routes data packets along networks. A network router connects at to the lowest degree two networks, commonly 2 LANs or WANs or a LAN and its ISP network. A router is often included as part of a network switch. A router is located at where one network meets another, including each point-of-presence on the Internet. A router has two key jobs:
- The router ensures that information doesn't go where it's not needed. This is crucial for keeping large volumes of data from clogging the network.
- The router makes sure that information does brand it to the intended destination.
In performing these two jobs, a router joins the two networks, passing information from one to the other and, in some cases, performing translations of various protocols between the two networks. It also protects the networks from ane another, preventing the traffic on one from unnecessarily spilling over to the other. This process is known as routing.
Routing is a role associated with the Network layer (layer 3) in the Open Systems Interconnection (OSI) model. Routers utilize network layer protocol headers, such as IP header where the source and destination addresses are included and routing tables to determine the best path to forward the packets. For the communication amid routers and decide the best route between any 2 hosts, routing protocols such as ICMP are used.
Actually, routers are specialized computers that send messages speeding to their destinations along thousands of possible pathways. One of the tools a router uses to decide which path a packet should go is a routing table. A routing table contains a collection of information, including:
- Information on which connections lead to item groups of addresses
- Priorities for connections to be used
- Rules for handling both routine and special cases of traffic
Information in the routing tables tin be static (with routes manually entered by the network administrator) or dynamic (where routers communicate to exchange connection and road information using various routing protocols). A routing tabular array can be as simple equally a few lines in the smallest routers, but tin can grow to massive size and complexity in the very large routers that handle the bulk of Net messages. Every bit the number of networks fastened to one another grows, the routing table for treatment traffic amongst them grows, and the processing ability of the router is increased.
DNS
DNS stands for Domain Name System. It purpose is to permit mapping between Internet names (eg : www.netvigilance.com) and IP addresses (eg : 97.eleven.12.13). It is based on a distributed network of proper name servers that allow the resolution of names in a hierarchical namespace, sharing the same "root". Therefore, The Domain Name System is a critical part of the Internet, because domain names are much 'more friendly' than raw IP addresses, a chip like Yellow Pages indexing Phone numbers confronting business names.
DHCP
Curt for Dynamic Host Configuration Protocol, a protocol for assigning dynamic IP addresses to devices on a network. With dynamic addressing, a device tin can have a different IP address every time it connects to the network. In some systems, the device's IP accost can fifty-fifty modify while it is nevertheless connected. DHCP also supports a mix of static and dynamic IP addresses.
Dynamic addressing simplifies network administration because the software keeps track of IP addresses rather than requiring an administrator to manage the task. This means that a new computer can be added to a network without the hassle of manually assigning information technology a unique IP address. Many ISPs apply dynamic IP addressing for punch-up users.
The DHCP is usually managed by the ADSL router on the network, or in the example of a larger network a domain server acting as DCHP for the network.
IPV4
IPv4 is the most widely used version of the Internet Protocol. It defines IP addresses in a 32-bit format, which looks like 123.123.123.123. Each 3-digit section tin include a number from 0 to 255, which means the total number of IPv4 addresses available is four,294,967,296 (256 x 256 ten 256 10 256 or ii^32).
Each estimator or device connected to the Internet must have a unique IP address in order to communicate with other systems on the Internet. Because the number of systems connected to the Internet is quickly approaching the number of available IP addresses, IPv4 addresses are predicted to run out shortly. When you consider that there are over half dozen billion people in the world and many people have more than than ane organisation continued to the Internet (for example, at home, school, piece of work, etc.), it is not surprising that roughly 4.3 billion addresses is not plenty.
To solve this problem, a new 128-bit IP system, called IPv6, has been developed and is in the process of replacing the current IPv4 system. During this transitional process from IPv4 to IPv6, systems connected to the Cyberspace may exist assigned both an IPv4 and IPv6 address.
IPV6
This led to the evolution of a new version of IP called IPv6 (IP version six), also known as IPng (IP new generation). Y'all will ask what happened to version 5. Well, it was developed, but remained in the domain of research. IPv6 is the version that is ready to be deployed over the whole Internet and exist adopted by all human beings (and whatever brute) using the Cyberspace and networks. IPv6 brings many improvements, mainly in the number of machines that can be accommodated on the Internet.
IPv6 Described
An IPv6 address consists of 128 bits, therefore allowing an astronomical number of machines. This is equivalent to the value of two raised to the power of 128, a number with nearly 40 trailing zeros.You must at present be thinking of the inconvenience of lengthy addresses. This is addressed too - IPv6 address accept rules to shrink them. Kickoff, the numbers are represented in hexadecimal instead of decimal numbers. Decimal numbers are numbers from 0 to ix. Hexadecimal numbers result from the group of bits in four, giving the following characters: 0, 1, 2, 3, 4, five, six, 7, viii, ix, A, B, C, D, E, F. An IPv6 accost is fabricated up of these characters. Since the $.25 are grouped in 4, and IPv6 accost will consist of 32 characters. Long, heh? Well, that'southward not and so serious, especially since there are conventions that help reduce the length of IPv6 address past compressing characters of repetition, for example.
An example of an IPv6 address is fe80::240:d0ff:fe48:4672. This 1 has only nineteen characters - there has been compression, something that goes beyond the telescopic of this article. Note that the separator has changed from the dot to the colon.
IPv6 not only solves the trouble of address limitation, but as well brings other improvements to the IP protocol, similar auto-configuration on routers and improved security, among others.
Transition From IPv4 to IPv6
The day when IPv4 will no longer be viable is coming, and now that IPv6 is effectually, the biggest claiming is to make the transition from IPv4 to IPv6. Imagine renewing the bitumen of a road under heavy traffic. There are many discussions, publications and research work going on and nosotros hope that when the time comes, the transition will piece of work out smoothly. This led to the development of a new version of IP called IPv6 (IP version half dozen), also known equally IPng (IP new generation). Y'all will ask what happened to version 5. Well, it was developed, just remained in the domain of research. IPv6 is the version that is ready to exist deployed over the whole Net and be adopted by all human beings (and whatever creature) using the Internet and networks. IPv6 brings many improvements, mainly in the number of machines that tin can exist accommodated on the Internet.
Source: https://www.rdcs.com/network-options.htm
0 Response to "What Is the Most Common Central Device Used Today to Connect Computers to a Network?"
Post a Comment